The Great Exposure: Why 2026 is the Year of the "Skill-less" Breach
The data from April 2026 is brutally honest: Your multi-layered defenses are no longer a deterrent. The AI upsurge has collapsed the barrier to entry for cybercrime. A teenage hacker with a basic LLM can now execute perfect spear-phishing and chain vulnerabilities that bypass your MFA. Discover the Forculus Verdict on the recent wave of Dutch breaches and why Inherently Resilient defense requires auditing the Path, not the Portal.
The Sovereign Provider Myth: Is "European" enough?
Is Open Source the answer, or can we trust Sovereign Providers? Stop asking if you can trust a tool or a partner. You can’t. True Digital Sovereignty is not about where your data is stored; it’s about where your control resides. In 2026, resilience isn't about finding the lowest price, it's about ensuring your Total Cost of Exit is lower than your Total Cost of Staying.
Mythos & The Glasswing Trap: Why Your “Minor” Bugs are Now Major Liabilities
The Era of "Minor" Bugs is Dead. In April 2026, the cybersecurity landscape has been split in two. On one side, Anthropic is claiming a "nuclear" breakthrough with its superpowered Claude Mythos. On the other, skeptics are calling it high-stakes theater to pad their IPO valuation.
The brutal reality lies in the data: Mythos isn't a "magic hacking button," but it has turned a months-long human exploitation process into a days-long autonomous one.
The "Double Agent" Crisis: The 2026 Resilience Pivot
The honeymoon is over. In 2026, we aren't just worried about what AI says, we’re terrified of what it does. As "Agentic AI" takes over corporate tasks, a new breed of "Double Agent" risk has emerged. If your AI agents have the keys to your kingdom, they might just be waiting for an external attacker to tell them to unlock the door.
The Strategic Autonomy Paradox
Sovereignty and resilience are the twin pillars of 2026 security, yet they often pull in different directions. Understanding how to build independent, indestructible infrastructure, without relying on global hyperscalers, is now the ultimate strategic advantage for the modern organization.
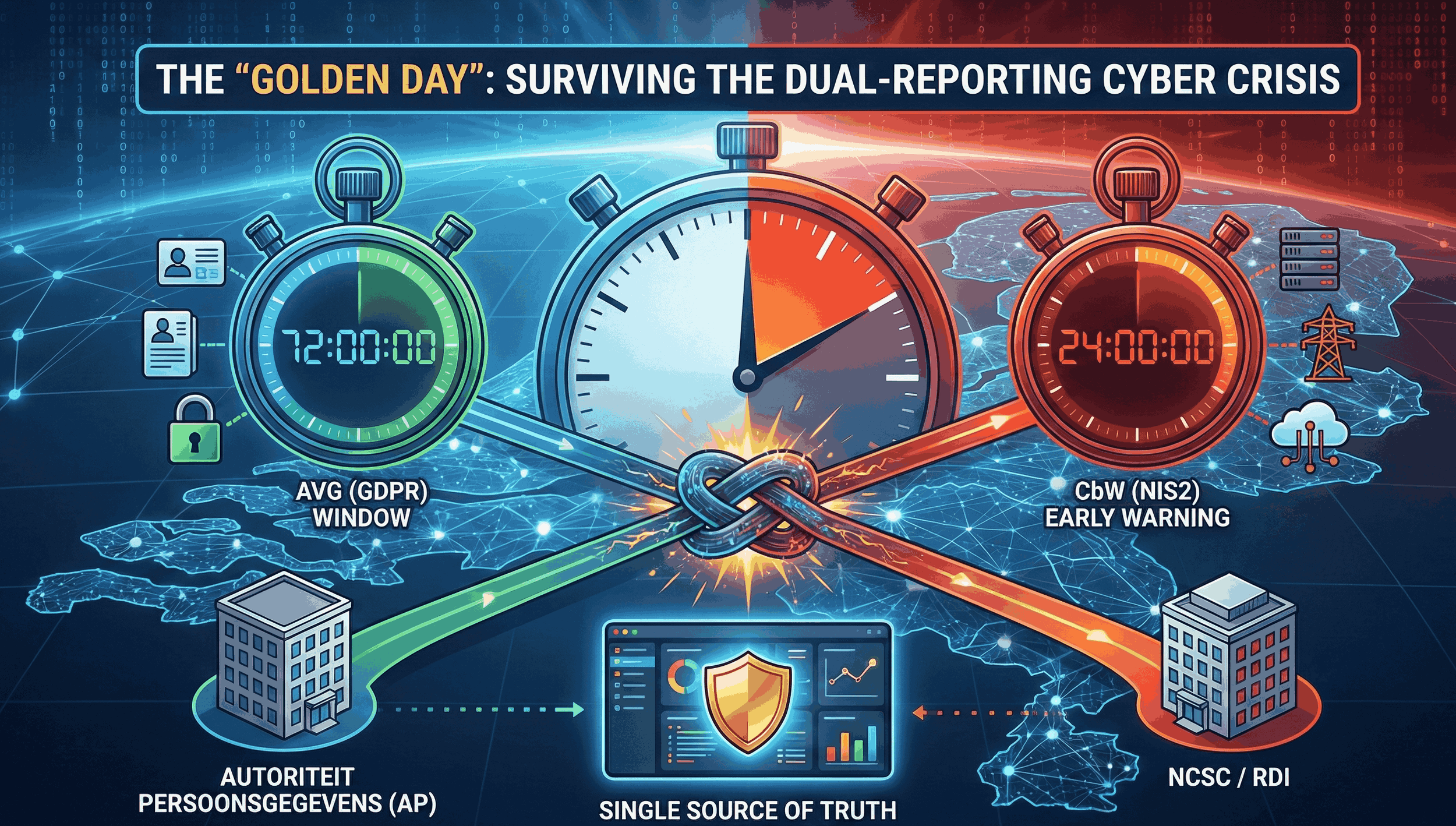
The 24-Hour Rule: Navigating the AVG and NIS2 Overlap
The biggest myth in Dutch cybersecurity is that you have three days to catch your breath after a breach. While the AVG (GDPR) gives you a 72-hour window, the new Cyberbeveiligingswet (CbW) has effectively deleted that luxury for thousands of Dutch companies.
The AI Hangover
In 2026, the AI honeymoon is officially over. As we shift from simple chatbots to autonomous "Agentic AI," the attack surface has fundamentally changed. From indirect prompt injection to the looming deadlines of the EU AI Act, organizations must now treat AI models as untrusted third-party software. It’s time to move past the hype and confront the "black box" liabilities currently sitting in your core infrastructure.
The NATO iPhone
The tech world is buzzing: Apple’s iOS 26 has officially entered the NATO Information Assurance Product Catalogue. But before you swap your ruggedized laptop for a standard iPad, understand the "Indigo" reality. Accreditation doesn't mean "secure by default", it means secure by lockdown. From mandatory biometric liveness checks to strict physical custody protocols, the iPhone is only as safe as the perimeter you build around it.
The New Standard: Navigating the ABRO 2026 Landscape
The era of "voluntary" security for Dutch government vendors has ended. With the full rollout of the ABRO 2026, every supplier from IT services to infrastructure is now a vital link in national security. This isn't just about passing a tender; it’s about a continuous lifecycle of trust verified by the NBIV. If you aren't ABRO-ready, you aren't just missing a contract; you're missing the new baseline for public sector partnership.
BIO2: the New Dutch Government Security Standard
As of January 1, 2026, the "baseline" has moved. The transition from BIO 1.04 to BIO2 (Baseline Informatiebeveiliging Overheid 2) is no longer just a technical upgrade, it is a legal evolution. For provinces, water boards, and the central government, BIO2 is now a mandatory framework for self-regulation, while for municipalities, it serves as the essential blueprint for meeting the Cyberbeveiligingswet (CbW).
ISO 27001 Certification
In the Dutch business landscape of 2026, ISO 27001 is no longer just a "nice-to-have" certificate for your lobby. With the Cyberbeveiligingswet (CbW) now in force, ISO 27001 has become the primary defensive shield for directors. It is the most robust way to prove you have met your legal "duty of care."
NIS2 Implementation in the Netherlands
The era of "voluntary" cybersecurity for Dutch businesses has officially ended. With the Cyberbeveiligingswet (CbW), the Dutch implementation of NIS2, expected to be fully active by Q2 2026, the stakes have moved from IT departments to boardrooms.